Protecting personal data and business information is becoming increasingly complex and important. The threat of an attack and the costs of a breach continue to rise, as does consumer mistrust. Businesses must face these challenges by establishing an information security plan to assess their vulnerabilities and prevent leaks of information.
What is an Information Security Plan?
An information security plan outlines how data is handled within your organization. It is a critical component of cybersecurity that helps you apply appropriate safety measures, address legal privacy requirements, and form a response plan for breach incidents.
Your information security plan will vary based on the specifics of your business but should provide, at least, a general guideline for data handling practices. You can add more detail and strictly enforce certain policies where necessary. Your plan should consider both human and technological threats, create a culture of information security, and plan for continuous improvement as technology and threats evolve.
Key Components of an Information Security Plan
There are many pieces that will need to come together to create a comprehensive information security plan. The goal is to maintain the integrity, confidentiality, and availability of your data while also averting potential threats.
Your information security plan should cover:
- The scope of your security controls and standards
- The classification of all data involved
- Specific instructions for emergencies
- Management objectives in case of a breach
- The consequences of non-compliance
In addition, the plan should also address the following key components:
Commitment – The leaders of your organization should provide input on security controls, ensure that all policies align with your company’s strategic direction, and demonstrate commitment to the security plan.
Screening – All individuals who will have access to your data should be properly vetted during the hiring process. Screening prevents security problems and reduces the risk of employees using data maliciously.
Policy – Your information security policies are the foundation of your plan. They should reflect your company’s overall security strategy for privacy protection.
How to Create an Information Security Plan
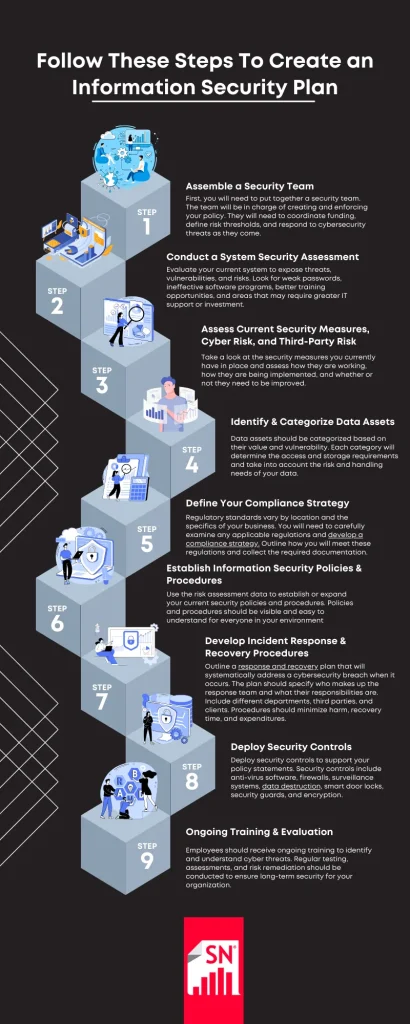
Step 1. Assemble a Security Team
First, you will need to put together a security team. The team will be in charge of creating and enforcing your policy. They will need to coordinate funding, define risk thresholds, and respond to cybersecurity threats as they come.
Step 2. Conduct a System Security Assessment
Evaluate your current system to expose threats, vulnerabilities, and risks. Look for weak passwords, ineffective software programs, better training opportunities, and areas that may require greater IT support or investment.
Step 3. Assess Current Security Measures, Cyber Risk, & Third-Party Risk
Take a look at the security measures you currently have in place and assess how they are working, how they are being implemented, and whether or not they need to be improved.
Examine how a cybersecurity breach would impact your business. Consider regulatory penalties, damage control procedures, and how your company would operate in the face of an incident. Create your plan based on the factors associated with your specific cybersecurity risks.
Third-party providers should also be assessed for risk. Any potential partners should comply with your list of requirements to work with your company.
Step 4. Identify & Categorize Data Assets
Data assets should be categorized based on their value and vulnerability. Each category will determine the access and storage requirements and take into account the risk and handling needs of your data.
Step 5. Define Your Compliance Strategy
Regulatory standards vary by location and the specifics of your business. You will need to carefully examine any applicable regulations and develop a compliance strategy. Outline how you will meet these regulations and collect the required documentation.
Step 6. Establish Information Security Policies & Procedures
Use the risk assessment data to establish or expand your current security policies and procedures. Policies and procedures should be visible and easy to understand for everyone in your environment. All employees should be required to follow the procedures and receive regular security awareness training.
Step 7. Develop Incident Response & Recovery Procedures
Outline a response and recovery plan that will systematically address a cybersecurity breach when it occurs. The plan should specify who makes up the response team and what their responsibilities are. Include different departments, third parties, and clients. Procedures should minimize harm, recovery time, and expenditures.
Step 8. Deploy Security Controls
Deploy security controls to support your policy statements. Security controls include anti-virus software, firewalls, surveillance systems, data destruction, smart door locks, security guards, and encryption.
Step 9: Ongoing Training & Evaluation
Employees should receive ongoing training to identify and understand cyber threats. Regular testing, assessments, and risk remediation should be conducted to ensure long-term security for your organization.
Why is an Information Security Plan Important?
An effective information security plan demonstrates compliance efforts and contributes to your organization’s overall success. You will benefit financially by avoiding fines and litigation for non-compliance, as well as avoiding the economic damage caused by a breach. Showing privacy concerns also builds trust with clients and gives you a competitive edge.
Boost Your Information Security Plan with Shred Nations Services
Shred Nations offers data and information management services to maintain compliance and increase security. We offer a wide range of solutions to keep your data safe and confidential. Contact us by calling (800) 747-3365 or filling out the form. We will connect you with local providers to help you build and implement data security that fits the needs of your organization.