When it comes to destroying sensitive documents, the list of what to shred is seemingly endless. Of course we all know about the obvious things like paystubs, tax records, and bank statements. But what about some of the more uncommon items that still need shredding? We spoke to a number of experts and business professionals about some of the items you may be neglecting to destroy properly.
The rule of thumb that every single person we spoke to agreed upon, was to shred anything that has personal identifiable information (PII) on it. The problem is that so many things in our daily lives contain snippets of information, it can be hard to know what’s dangerous and what isn’t. You may be surprised to learn that criminals don’t need a lot of information to make a few guesses about your life.
Uncommon Items You Should be Shredding
Identity thieves and cybercriminals have many ways to steal information. There’s no reason for us to make their jobs any easier. In fact, one of the easiest methods of obtaining your PII is still going through your trash. In case you didn’t know, trash picking is legal in all 50 states. As unsophisticated as this may seem, our trash can give strangers a great deal of personal information that can be very compromising in the right hands.
1) Junk Mail

Who among us doesn’t get targeted advertisements and credit card offers on a weekly basis? The truth is that most of us pay little to no attention to these letters that often contain heaps of information about us. It can be tempting to throw these items into the trash without a second thought, but this can be very dangerous. Aside from the fact that your name and address are right on the envelope, there can be even more compromising information within.
Joel Jackson, co-founder of Lifeforce, went on to elaborate. “Credit card applications must be shredded. They are routinely thrown away, sometimes in a trash receptacle next to the group of mailboxes at an apartment complex. There have been cases of people digging through the garbage for those applications and filling them out under assumed names – the very names shown on the front of the envelope.”
“After a little more sleuthing, often inside the same trash can, an identity thief can get all he or she needs to open a line of credit and go on a spending spree – in your name.”
2) Birthday Cards & Birthday Offers
At first glance, these may seem harmless. However, having your name, address, and birthday can be pretty dangerous information in the hands of a thief. With a few educated guesses, thieves can piece together enough data to open lines of credit, or obtain sensitive information from third parties.
Rob Bartlett, Founder and CEO of WTFast.com writes “you should shred any advertisements from companies wishing you a happy birthday or offering you a special birthday deal. Our birthdays too often remain easily-accessible to potential identity thieves, but there’s no reason to make it any easier for anyone rifling through your garbage.”
“Connecting a person’s birthday with other information found in the trash can potentially give access to key medical records, prescriptions, and even bank information. For that reason, shred any ads identifying your birthday.”
3) Flight and Travel Related Documents

This one might come as a surprise as well. In fact, the expert we spoke to proposed a pretty frightening scenario. Patrick Casey, Director of Growth Marketing at Felix Health mentioned ” It’s easy to get caught up in the excitement of going on vacation, but don’t forget to take proper care of flight-related documents before taking off. This includes your boarding pass, car rental information, a scan of your passport, and any other documents you might need.”
“There’s no telling what fraudsters might do if they find this information. Fraudsters could use it to compromise your account, gain access to your bank details, and possibly even book a flight under your name. On top of that, they may attempt to burgle your house while you’re away if they know the date and duration of your vacation.”
4) Pet & Veterinary Paperwork

We all love our pets, and just like us, they need medical care from time to time. Don’t be fooled, although your pet is the one getting the attention, it’s your name and payment information on the documents. Not to mention that fact that many people use pet names as passwords or verification questions.
Mila Garcia, Co-founder at iPaydayLoans.com mentioned “While your pet doesn’t have any online accounts that could be hacked, there’s a chance that you may be using your pet’s name as your password, like many people have a tendency to do. And even if you don’t, chances are you probably use it as a password verification answer. Most of the time, that’s fine, since it’s something that can be very hard for strangers to guess. However, failing to shred medical papers that include your pet’s name may end up in the hands of identity thieves who may be looking to hack your account.”
5) Sticky Notes & Post-Its
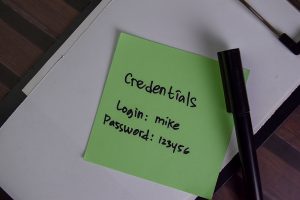
It’s a known fact that many people take phone messages, or even write down passwords on sticky notes near their desks. But what did you do with it when it was no longer needed? Did you crumple it up and throw it in the trash? These quick, often thoughtless, notes can be a huge hazard to information security.
Adam Garcia, Owner of The Stock Dork said “Post-it notes are a must-have item in any office. When on a call or interacting with a coworker, they are easy to grab and write down information. Passwords, account numbers, and other sensitive information are frequently scrawled on these notes. However, when they are no longer required, they are frequently discarded. Instead, shred these notes to protect yourself.”
It takes no time at all to put these into the shredder or shred bin like you would any other sensitive document. Depending on what’s written on the note, it may be even more compromising that a spreadsheet or fiscal data.
6) Photos
 This one may not seem that obvious at first. However, many search engines including Google, allow you to search or index images these days. That means that scanning a photo and putting it into a search engine might turn up other personal information. This action could lead to anything from social media accounts, to business profiles. Other information might be available too, just by looking at the other contents in the trash.
This one may not seem that obvious at first. However, many search engines including Google, allow you to search or index images these days. That means that scanning a photo and putting it into a search engine might turn up other personal information. This action could lead to anything from social media accounts, to business profiles. Other information might be available too, just by looking at the other contents in the trash.
Dr. Frederik Lipfert, Founder & CEO of VPNCheck.org says “photos of employees, customers, and suppliers may appear innocuous, but fraudsters might use them to create an identity. When you combine this with any other personal information they may have obtained from your company, you might be in big danger. Instead of throwing these images away, destroy them to keep your employees and customers safe.”
7) Receipts from Stores and Retail Establishments
 Receipts from retailers may have your name and often the last four digits of your credit card. This could give cybercriminals a head start when it comes to piecing together a full credit card number, name, or address. Especially if it’s found in your trash.
Receipts from retailers may have your name and often the last four digits of your credit card. This could give cybercriminals a head start when it comes to piecing together a full credit card number, name, or address. Especially if it’s found in your trash.
Even more alarming is the fact that it may lead to social engineering attacks or crimes that aren’t virtual in nature. Your receipts can potentially expose spending habits, and even specifics regarding age, gender, or work status.
Kelvin Stewart, the co-founder of USBadCreditLoans.com says “receipts contain valuable information about what kinds of purchases you make. For example, if someone knows you buy diapers for infants or tampons every month, they could guess that a child lives in the house or there’s someone female living there who may not be home often enough (e.g., because she works full time). They could use this information to plan a theft or kidnapping.”
8) Mail or Offers with QR Codes
 QR codes have become the new norm for everything from restaurant menus to buying cryptocurrency. They can be a wonderful shortcut when trying to direct a consumer to a particular website. On the flip side, they can also lead you to some nefarious sites that may be less than reputable.
QR codes have become the new norm for everything from restaurant menus to buying cryptocurrency. They can be a wonderful shortcut when trying to direct a consumer to a particular website. On the flip side, they can also lead you to some nefarious sites that may be less than reputable.
Mark Pierce, CEO of Cloud Peak Law Group writes “one very important item you should be shredding is papers with QR codes. These are usually quick links to apply to something like a credit card or a loan, and are already pre-filled in with your information. This, coupled with your name and address, could be enough for a scammer to open a fraudulent account.”
9) Shipping Labels, Return Labels, Packing Slips
 It’s safe to say that almost all of us use some form of online shopping these days. Especially after the last few years, online shopping has become more and more common. Many packages, especially for clothes or shoes come with return labels already filled out. These labels could have all sorts of information you wouldn’t want in the hands of strangers.
It’s safe to say that almost all of us use some form of online shopping these days. Especially after the last few years, online shopping has become more and more common. Many packages, especially for clothes or shoes come with return labels already filled out. These labels could have all sorts of information you wouldn’t want in the hands of strangers.
Adam Ng, the CEO and Founder of Trusted Malaysia mentions “shipping label in that box with your new shoes? If it has a little plastic pouch with an insert in it, like a receipt, an order form, or a confirmation, it likely has personally identifiable information. Double check your boxes before you recycle or reuse them, pull out any shipping labels or inserts.”
10) USB Flash Drives
 Although a USB drive isn’t made of paper, these devices should still be destroyed to avoid data leakage. Many of our shredding providers also dispose of electronics that contain sensitive data. In many ways, USB drives are even more compromising than lost documents. USB drives can hold hundreds, if not thousands of sensitive files. In addition to documents, these drives may also contain photos and videos.
Although a USB drive isn’t made of paper, these devices should still be destroyed to avoid data leakage. Many of our shredding providers also dispose of electronics that contain sensitive data. In many ways, USB drives are even more compromising than lost documents. USB drives can hold hundreds, if not thousands of sensitive files. In addition to documents, these drives may also contain photos and videos.
Austin Dowse, CEO of Aimvein says “this isn’t just about paper, it’s also about destroying your data as well. It includes USB drives, flash drives, USB drives, and other devices for media like computers with possibly sensitive data. Even if the devices or drives are wiped clean, PII is still accessible in the hands of criminals with easy-to-use software who are adept at stealing information. A study conducted in 2017 by the National Association of Information Destruction (NAID) discovered that 40 percent of devices that were resold were stuffed with PII which included passwords, usernames, and credit card data. The information could be retrieved by criminals, and it’s much simpler than you think.”
Shred Nations can Help Keep You Safe with Secure Shredding
Although the list above contains a few examples of uncommon items to shred, there are dozens more. When in doubt, shred it. It’s better to be safe than sorry when it comes to protecting your identity, or your business. Shred Nations has helped over 1 million people with their shredding projects, and we can help you too.
Just give us a call at (800) 747-3365, or simply fill out the form on this page to get a free quote today! We’re here to answer any questions you may have, and we’re dedicated to finding the right service for your needs.












