Dumpster diving might sound humorous at first. Until you realize the real-life security risks involved. Many people aren’t aware that dumpster diving or trash picking is largely legal in all 50 states. We spoke to NYU professor, and 20-year cybersecurity veteran Pieter VanIperen about the risks and dangers of dumpster diving can have on data security. As an instructor and managing partner at PWV Consultants, Pieter has a section of his course devoted entirely to this practice. Watch our video interview or read the full blog below.
Legality of Dumpster Diving
Not only is dumpster diving mostly legal, but it’s also a common practice these days. Pieter explains that it’s typically only illegal in rare circumstances where local ordinance prohibits it, or you’re trespassing to gain access. “Here’s the thing though, in most places there’s a trash pickup day where all your trash needs to be moved to the curb for pickup. Once trash is on the curb it’s technically public property” he says.

There’s also legal precedent to back up what he’s saying. A 1988 Supreme Court case (State of California vs. Greenwood) states that searching through the trash is legal as long as it doesn’t go against any city, county, or state ordinances. Once trash is on the curb, or in your driveway, it’s public domain. This means that anyone who wants to look is free to search through your trash.
What’s more, in a lot of these places where trash picking is prohibited by ordinance, it’s really only a slap on the wrist. If the thief is not worried about the $250 fine, they might do it anyway. So make sure you’re not throwing away anything too sensitive.
Criminal and Law Enforcement Applications

Surprisingly, both applications are really similar. Criminals use dumpster diving for a variety of exploits from identity theft to social engineering attacks. Law enforcement and intelligence agencies have used trash in evidence gathering and dossier building for years.
Furthermore, you can get a really clear picture of someone’s life from what they leave behind. Even something as simple as where they order food from, what foods they may like or dislike, or where they shop. You can piece together a decent amount with just some reasonable guessing. Everything from where they’ve been, who they’re seeing, and when. Thieves can use all of this information against an individual.
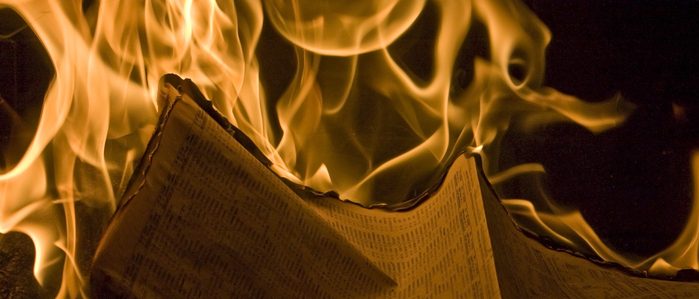
Dumpster Diving is a Real Threat

Perhaps the most alarming threats come in the form of ransom attacks and social engineering. These attacks typically fall into two categories. First is the angle of using information to construct a scenario where a person is duped into giving up critical information. “You were at so-and-so’s place and left something….Give me some information and I’ll get it back to you.” Second and perhaps most alarming is the leverage angle. Applying pressure to force an individual into taking some kind of action. Similar to blackmail.
Pieter says “Look, I’m a parent…could someone go through my trash and find kid’s stuff? Diapers, paperwork from the school, etc? One avenue of attack might be that something is going on at the school. However, another avenue might be that if you don’t do this thing for me, I’ll do something for your kid. These threats may be oceans away, but you don’t necessarily know that.”
The information that thieves can retrieve from the trash is potentially dangerous. “I teach this in my course, and it’s been taught in every course I’ve ever taken on intelligence gathering,” Pieter says. “I think it’s important for your audience to understand that this is a real thing that happens regularly. It’s not some freak occurrence.”
Protect Yourself From the Dangers of Dumpster Diving Today
Shred Nations partners with some of the most secure document and IT asset destruction companies in the data destruction business. We can help you find the service that’s right for your business or personal needs. Start the process now by filling out the form, using the live chat option, or calling us at (800) 747-3365. You’ll receive a response in minutes from top specialists in your area. Don’t leave your security to chance with the dangers of dumpster diving. Call us today.